Bypatrol Policy Guide
About
Our policy guide is a simple checklist for stopping Chromebook exploits from the Google Admin Console. It blocks bugs from the last 30+ ChromeOS versions to keep students safer online.
To further secure your district's Chromebooks, install the Bypatrol extension to stop exploits and proxies the smart way.
The policies in this section are for admin.google.com. They should be set up by a GSuite admin.
Student policies
Location: Devices > Chrome > Settings > User & browser settings
Ensuring proper enrollment
Policy name: Enrollment permissions
Recommended value: Only allow users in this organization to re-enroll existing devices (cannot enroll new or deprovisioned devices)
Disabling task manager
Policy name: Task manager
Recommended value: Block users from ending processes with the Chrome Task Manager
Disabling incognito mode
Policy name: Incognito mode
Recommended value: Disallow incognito mode
Stopping certificate tampering
Policy name: User management of installed CA certificates
Recommended value: Disallow users from managing certificates
Preventing SSL spoofing
Policy name: SSL error override
Recommended value: Block users from clicking through SSL warnings
Blocking DNS-over-HTTPS
Policy name: DNS-over-HTTPS
Recommended value: Disable DNS-over-HTTPS
Blocking exploit URLs
Policy name: URL blocking
Recommended value:
chrome://kill
chrome://crash
chrome://checkcrash
chrome://badcastcrash
chrome://memory-exhaust
chrome://hang
chrome://shorthang
chrome://extensions
chrome://settings/signOut
chrome://os-settings/osSignOut
chrome://network
chrome://net-export
chrome://net-internals
chrome://sync
chrome://sync-internals
chrome://prefs-internals
chrome://serviceworker-internals
chrome-untrusted://crosh
chrome-extension://nkoccljplnhpfnfiajclkommnmllphnl
chrome://inspect
chrome://flags
javascript://*
filesystem://*
Google says not to disable system features via URL blocking, but URL-blocking is just the best way -- Blocking the Crosh terminal with Google's "disabled system features" option, for example, will still allow use of it in versions older than Chrome 99, where vulnerabilities exist. In general, it’s best to block URLs with the URL blocklist settings.
Disabling inspect
Policy name: Developer tools
Recommended value: Never allow use of built-in developer tools
Preventing login confusion
Policy name: Multiple sign-in access
Recommended value: Block multiple sign-in access for users in this organization
Blocking guest mode
Policy name: Browser guest mode
Recommended value: Prevent guest browser logins
Enabling proper accessibility options
Policy name: Accessibility options in the system tray menu
Recommended value: Show accessibility options in the system tray menu
Device policies
Location: Devices > Chrome > Settings > Device settings
Forcing enrollment
Policy name: Forced re-enrollment
Recommended value: Force device to automatically re-enroll after wiping
Disabling guest mode
Policy name: Guest mode
Recommended value: Disable guest mode
Restricting logins
Policy name: Sign-in restriction
Recommended value: Restrict sign-in to a list of users
The value for this policy should be set to *@domain.com, where domain.com replaced by your district's domain. Make sure to include staff domains if they are seperate.
For example:
*@myschool.edu
*@myteachers.edu
Ensuring that policies are always active
Policy name: Device off hours
Keep this section blank; don’t use any off hours for your student Chromebooks.
Ensuring proper device updates
Policy name: Auto-update settings
Policy sub-name: Release channel
Recommended value: Stable channel
Policy name: Auto-update settings
Policy sub-name: Updates over cellular
Recommended value: Allow automatic updates on all connections, including cellular
Blocking kiosk escape exploits
Policy name: Kiosk spoken feedback
Recommended value: Disable spoken feedback
This policy helps mitigate an exploit prior to Chrome 120 which allowed for a user to browse in a completely unrestricted browser.
App and extension policies
Location: Devices > Chrome > Apps & extensions > Users & browsers
Limiting app installations
1: Click "Additional Settings" in the top right corner.
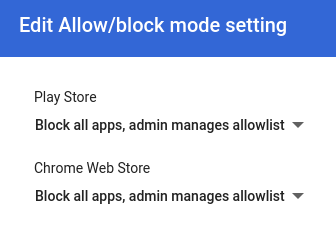
2: Click "Edit" in the "Allow/Block mode" section.
3: Make sure both the Play Store and Chrome Web Store options are set to "Block all apps" by default.
Network Settings
Location: Devices > Networks
Blocking VPNs
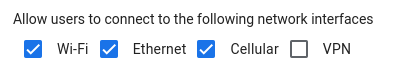
1: Scroll down and click "General settings".
2: Scroll down and click "Allowed network interfaces".
3: Uncheck the VPN option, and save.
Next steps
Not all exploits can be blocked by Google Admin Console policies. With the Bypatrol extension -- currently free and in open beta -- it's easy to:
- Block hundreds of proxy sites the smart way
- Patch specific ChromeOS and filter vulnerabilites that are often abused
- Block WebView bypasses in apps
- Monitor the frequency of exploits in your district (coming soon)
For more info, check our homepage.
Install the extension for your district
Contact us
Did we miss anything? Let us know
Admins: Do you have any questions about our policy guide? Contact us
Want to get updated when our policy guide changes? Join the mailing list